Unlock the value already in orbit
A secure payload operating system that turns idle on-board compute into new revenue. Build, deploy, and update satellite apps the way cloud engineers ship to production.
How we fit
A payload platform, not a flight software replacement
Runs on the payload side
SpaceOS lives in its own partition on the payload computer. Your bus software, attitude control, and any real-time or safety-critical system stays exactly where it is.
Works with the hardware you fly
Hardware-agnostic by design. Validated across 8 on-board computers and multiple hypervisor substrates. No new flight-qualified avionics required.
We share in the upside
No upfront cost to the operator. We participate only in measurable value: incremental revenue from new workloads, or cost savings from on-board processing.
How much value is sitting idle in orbit?
Even high-performing satellites are only fully productive when positioned over the right area. The rest of the orbit, the payload computer has capacity no one is using.
Idle on-board compute
On-board processors are sized for peak mission needs and then sit underused most of the orbit. NASA JPL data puts average in-orbit compute utilisation near 10%, which represents roughly $5B per year of capacity operators cannot currently monetise.
Frozen at launch
Payload software is written once, per satellite, before launch. Adding a new application afterwards is a custom integration that takes months, if it is possible at all. Missions built for one customer rarely adapt to the next.
Cyber risk blocks new revenue
No operator will host someone else's code on a flight computer without isolation they trust. A single faulty or malicious app can lose the satellite. Without a safe way to run third-party workloads, the spare capacity stays unreachable.
A payload OS, not a flight software replacement
SpaceOS boots in its own partition on the payload computer, where mission applications run. It never touches bus management, attitude control, or any safety-critical, real-time system. Your flight software stays exactly where it is.
What SpaceOS does change is the bespoke, one-off payload code that makes every mission a custom integration. Applications are packaged once, run across fleets, updated safely, and isolated from each other on the same hardware.
Think of it as a CI/CD pipeline and app store for satellites you already own, with hardware-backed isolation strong enough to safely host third-party workloads.
On-board architecture
Two partitions on one payload computer
Bus partition
Your flight software, untouched
- ● Bus management, attitude, thermal, power
- ● Real-time control loops
- ● Your existing RTOS and flight code
- ● Safety-critical, mission-qualified
Payload partition
Where SpaceOS runs
- ● Mission applications, isolated from each other
- ● Update and rollback lifecycle (A/B partitions)
- ● App store for first- and third-party workloads
- ● Non-real-time by design
Built to run alongside, not replace
Four capabilities operators need from a payload platform: safe co-existence with flight software, strong isolation between apps, a lifecycle that survives intermittent links, and cryptography built for the next two decades.
Payload-only, non-real-time
SpaceOS boots in its own partition on the payload computer. Bus, attitude, thermal, and power control stay on your existing flight OS. Real-time loops are never interrupted by application workloads.
Hardware-backed isolation
Applications run as single-address-space VMs under KVM, Xen, or Muen. Hardware enforces separation between apps and between payload and bus. A radiation-induced memory upset, a crashing app, or a malicious workload stays contained in its own partition and cannot ripple through the rest of the system.
CI/CD lifecycle for orbit
Build, sign, push, deploy, monitor, and roll back the way cloud teams ship to production. A/B partition scheme and content-addressable updates make bad deployments safe to reverse, even over 4 kbit/s links.
20× smaller footprint
10 MB application images instead of 250 MB container stacks. Smaller images mean faster uplinks, cheaper hardware, and a far smaller attack surface. Validated bit-for-bit against Thales Alenia Space workloads.
What operators are unlocking
Three value streams, on hardware already in orbit: processing data on-board, hardening payloads against cyber risk, and hosting third-party apps as a new revenue line.

On-board AI processing
Validated with Thales Alenia Space
Run inference on-board, downlink insights instead of raw images. Same AI model, 20× smaller footprint, up to 37% faster inference. Turns an idle payload processor into a downlink-cost saver.
Read more
Cyber-resilient payloads
Zero sandbox escapes in HACKSAT'25
Hardware-backed isolation, memory-safe code, post-quantum crypto. 34 participants, 8 weeks, zero sandbox escapes. Built for defence, government, and critical infrastructure missions.
Read more
Satellite app store
ESA-backed, launching with OHB Hellas
Monetise unused compute capacity. Third-party apps run safely on your satellite with strong isolation. New revenue streams without launching new hardware.
Read moreSee SpaceOS in Action
Two interfaces on top of the same payload platform: a familiar CLI for developers shipping new apps, and a marketplace for operators opening idle compute to paying workloads.
Build, test locally, deploy to orbit. The same workflow cloud teams already use to ship to production.
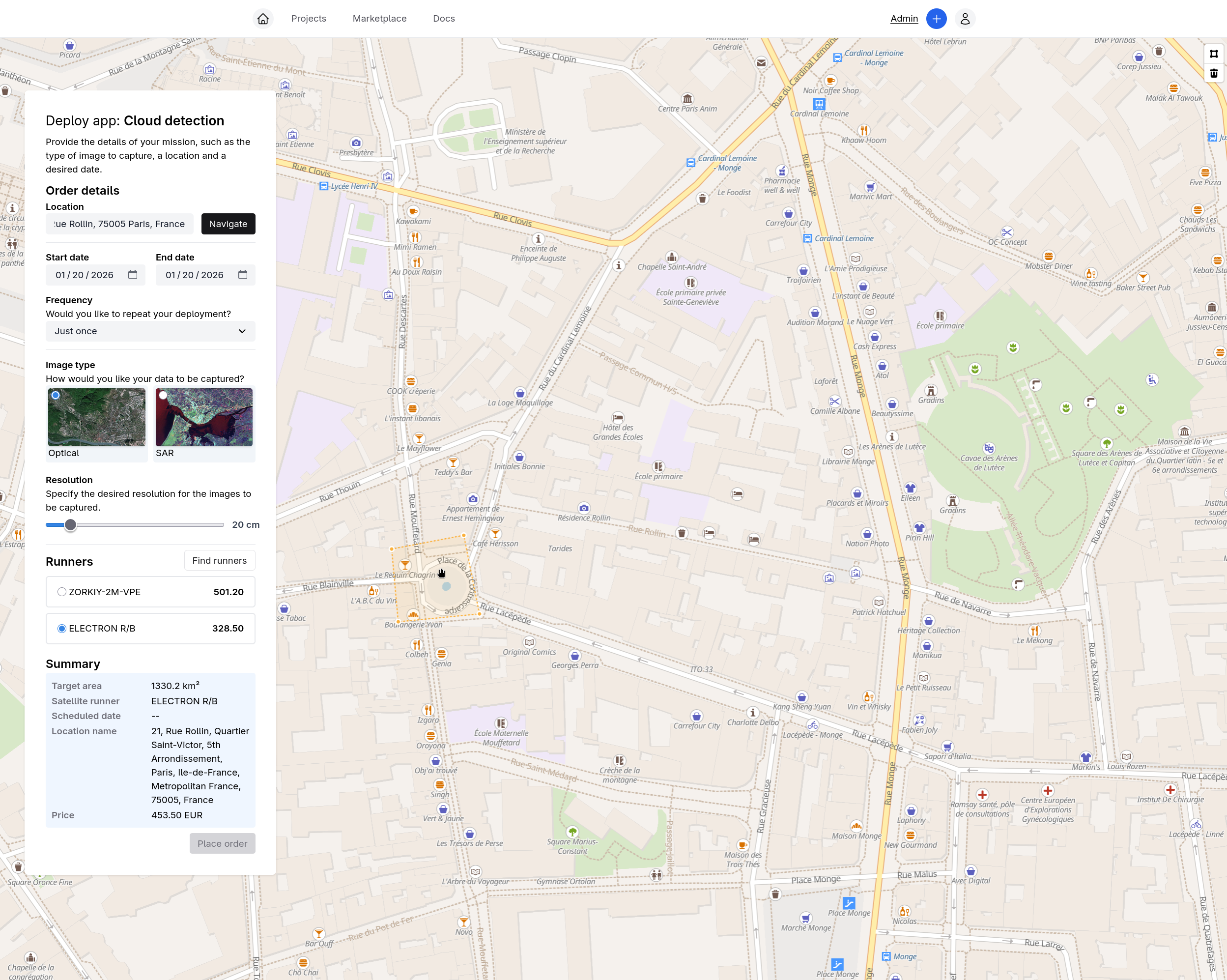
Draw your area of interest, pick an app, compare satellite runners. On-board processing cuts downlink costs by up to 7×.
Built with the people already running satellites
SpaceOS is developed and deployed with aerospace partners across Europe, the U.S. and Australia. SpaceOS reached orbit in March 2025 on Clustergate-1 and again in March 2026 on Clustergate-2.
Funded partnerships
EUR 1.5M+ in funded project commitments across ORCHIDE (Horizon Europe, with Thales Alenia Space), CEOS (BPI France 2030), and OSIP (ESA marketplace demonstration).
We are working with Innoflight to offer SpaceOS alongside their CFC-400XS flight computers. OHB Hellas provides the hardware platform for a joint satellite app store project.
Read about Innoflight partnership →Flight path
First payload launched March 2025 on SpaceX Transporter-13. Clustergate-2 launched March 2026, demonstrating the CCSDS protocol stack with OTA rekeying in orbit.
Mission operators across Europe and the U.S. are evaluating SpaceOS as their payload platform. Parsimoni was selected for the Techstars Space Accelerator (Fall 2025) and the Starburst Paris accelerator. The company has offices in France and California, with further locations planned across the U.S. and Europe.
Read about our first launch →How we engage
We take the integration risk. Operators keep their satellites, their hardware, and their flight software. We participate only in the new value we help unlock.
We integrate at our expense
Getting SpaceOS running on an operator's payload is our investment, not theirs. No integration fee, no licence minimum, no risk of shelfware.
Participation tied to value
A 10 to 15% platform fee on the new revenue operators earn from third-party workloads, or the savings they see from on-board processing. If it doesn't pay, we don't get paid.
Your hardware, your flight software
SpaceOS adds a layer on top of what you already operate. No migration of bus software, no new flight-qualified avionics, no lock-in.
Technical Resources
Deep-dive documentation for technical evaluators. Contact us for early access.
SpaceOS Technical Overview
Coming SoonArchitecture, Benchmarks, CCSDS Stack, Cryptography
Deep-dive into SpaceOS internals: unikernel runtime, up to 20× smaller footprint than K3S, formally verified cryptography, and the CCSDS protocol stack with 60+ fuzz targets.
SpaceOS and Docker
OCI Compatibility Guide
How the Docker workflow maps to satellites. What transfers, what doesn't. Migration guide for container teams.
Security Architecture
Formal Verification & PQC
Post-quantum cryptography, memory safety, hardware isolation. TCB analysis and threat model for security-critical missions.
Frequently Asked Questions
Common questions from operators, investors, and technical evaluators.
No. SpaceOS is a payload operating system. It runs in its own partition on the payload computer, where mission applications live. Bus management, attitude control, thermal, power, and any other safety-critical or real-time system stays exactly where it is today. SpaceOS is non-real-time by design.
Three things. First, it runs applications on the payload computer with hardware-backed isolation, so multiple apps (including third-party ones) can share the hardware safely. Second, it provides the update and rollback lifecycle operators need to ship new code to orbit: build, sign, push, deploy, monitor, reverse if it misbehaves. Third, it powers an app store that lets operators turn idle compute capacity into new revenue from third-party workloads.
Payload computers capable of running a Type-1 hypervisor (KVM, Xen, or Muen). Validated on 8 on-board computers across ARM and x86 so far, including flight hardware. SpaceOS is hardware-agnostic by design: no new flight-qualified avionics are required to adopt it.
SpaceOS is at TRL 6: system prototype demonstrated in a relevant environment, with two payloads in orbit via DPhi Space's Clustergate missions. Formal qualification under ECSS-Q-ST-80C is typically led by a prime contractor and scoped to a specific mission. The building blocks have production heritage: the network stack ships in Docker Desktop; the cryptography ships in Chrome and Android via BoringSSL. The integration is new, the components are battle-tested.
Payload applications run as single-address-space VMs under a Type-1 hypervisor, with separation enforced by the hardware rather than by kernel namespaces. In HACKSAT'25, an adversarial security challenge, 34 participants spent 8 weeks attempting to escape the sandbox and attack other applications, with roughly a thousand executions. None succeeded.
Unlock the value already in orbit
If you run a satellite fleet, build payload hardware, or ship space applications, we'd like to compare notes. No upfront cost, no change to your flight software. We take on the integration risk.
Get in TouchContact Us
Interested in SpaceOS? Let's talk.